When an event agency manages both a pharmaceutical client and a financial services client, their primary concern is not platform features, but whether they can guarantee complete data separation between clients.
There are two possible answers. One relies on access controls and separate user accounts. The other ensures that the architecture makes data commingling structurally impossible.
These answers are fundamentally different. The first is a policy, while the second is a guarantee. For agencies in regulated industries, only the latter stands up to scrutiny.
This post explains how we built multi-tenancy into Virtrio at the architectural level, not as a configuration layer on a shared data model, but as a foundational constraint extending from the browser token to the database schema.
The Problem with Soft Multi-Tenancy
Most platforms that claim multi-tenancy implement what the industry calls soft multi-tenancy: a single data model shared by all customers, with a tenant identifier column in each table to filter records at query time.
In practice this looks like: SELECT * FROM Events WHERE Client = JSES893slasfl-asldjaAd. Client A sees only their records, and Client B sees theirs. However, all data resides in the same tables, on the same database, managed by the same application logic. Every service, in every code path, correctly applies that filter. One missed WHERE clause — in a reporting query, an analytics aggregation, a bulk export — and data crosses the tenant boundary. Not dramatically. Not visibly. Quietly, in a log file or a report row that shouldn't be there.
Soft multi-tenancy works. Soft multi-tenancy is effective until it fails. In regulated industries, such failures result in data breaches, not just support issues.
Hard multi-tenancy: What It Actually Means
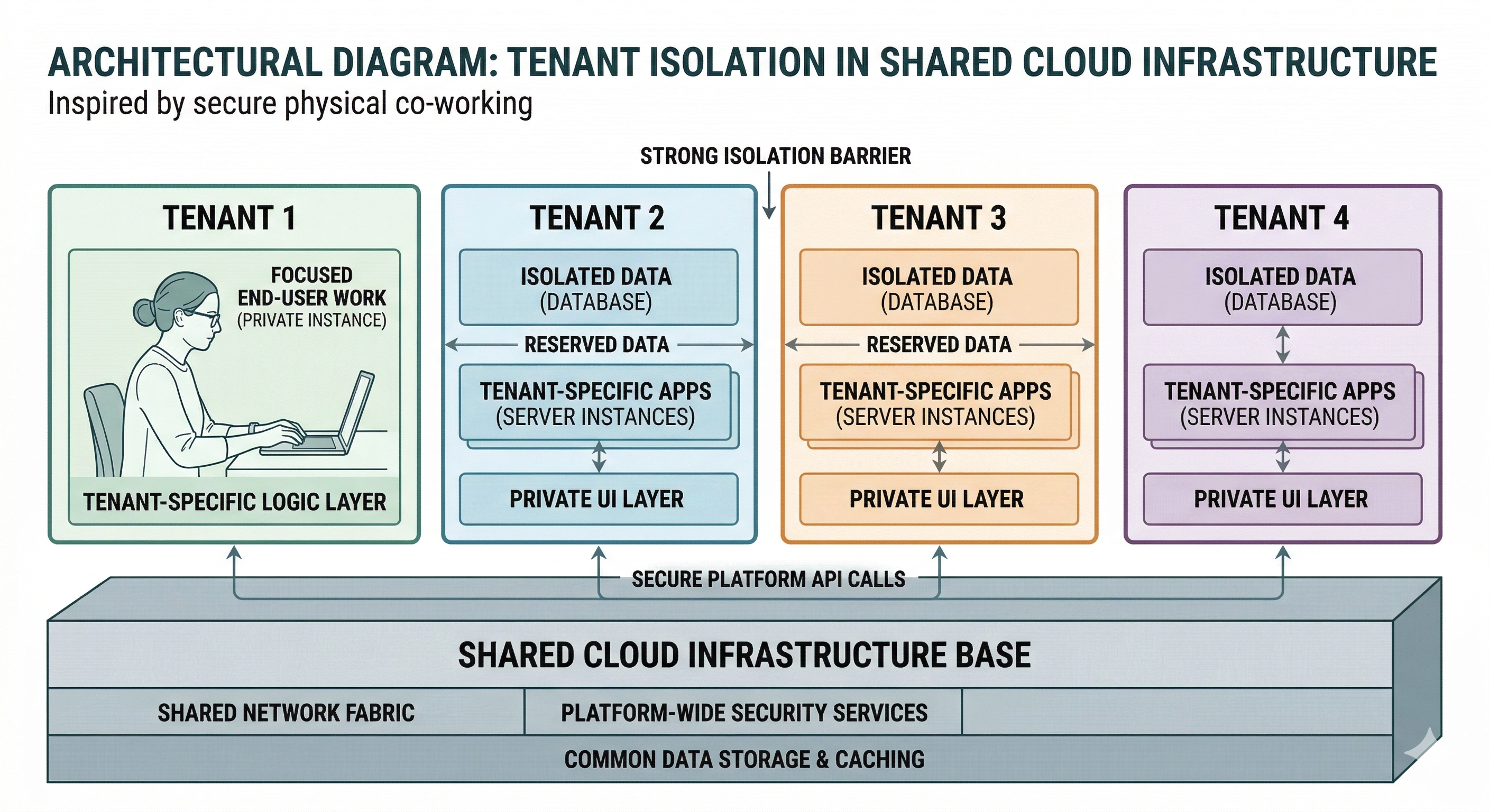
Hard Multi-tenancy means the architecture enforces isolation, rather than relying on application logic for consistent enforcement.
In Virtrio, this is achieved through two integrated layers: the identity layer, which cryptographically scopes each request to a tenant before accessing data, and the schema layer, which physically separates data across domains in the database. Together, they make tenant boundary violations structurally impossible rather than merely unlikely.
Layer One: JWT-Scoped Tenancy at the Identity Boundary
Every authenticated request in Virtrio includes a JSON Web Token issued by the Identity service. This token is not a generic session credential; it is a cryptographically signed assertion that encodes the user's tenant, role, and event-level permissions at issuance.
The tenant identity is embedded in the token and cannot be altered by the client or elevated through request parameters. It is signed with a key the client does not possess, and every downstream service validates the signature before processing requests.
The token serves as the enforcement mechanism. It is not a middleware setting or session variable, but a cryptographic proof of tenant identity that accompanies every request and is independently verified by each service.
This means that a user authenticated to Tenant A cannot access Tenant B's data, regardless of the URL or request body. The token does not permit it, and the service will not execute such requests. No code path allows cross-tenant data access. Upon provisioning a new client, a new tenant is created in the Identity service. That tenant gets its own isolated workspace — its own branding configuration, its own event catalogue, its own registration data, its own team members. The agency administrator can see and manage all their tenants through a single master view. Each tenant sees only its own environment. The boundary between them is enforced by the token's cryptographic scope, not by UI restrictions that could be circumvented.
Layer Two: Schema-Level Isolation in the Database
The second layer operates at the database level. Virtrio runs many microservices, each responsible for a distinct domain. Each service maintains its own schema.
This separation is not merely organisational. The registration service cannot directly access the engagement schema, and the catalogue service cannot access the identity schema. Cross-domain data access occurs only through explicit gRPC service calls, which include the JWT token and undergo the same authorisation validation as client requests.
A query in the registration service cannot inadvertently access data from the engagement schema due to a missing filter. Schemas and services are separated, and the only permitted communication channel is typed, authenticated, and auditable.
Within each schema, tenant scoping is enforced at the query level. Unlike soft multi-tenancy, where this filter is the sole isolation guarantee, here it is the third line of defence after the token and schema boundaries. A missed filter does not cause a breach; it results in an empty result set because the request lacks the required token scope.
What This Means for Regulated Deployments
As a result, an agency can support both pharmaceutical and financial services clients on the same infrastructure without risking data segregation failure.
The pharmaceutical client's registration data, engagement analytics, and attendee records are stored in their tenant. The financial services client's data remains within their own. The shared infrastructure, including compute, database instance, and caching layer, is invisible to both. Each experiences a fully isolated environment, and their data never overlaps.
This matters in regulated industries for reasons beyond compliance. It influences how agencies present their services to clients. A platform that demonstrates hard multi-tenancy at the architectural level, as a verifiable property rather than a claim, enables a fundamentally different commercial discussion compared to one that relies on access controls and operational discipline.
It also affects the agency’s own liability posture. When a client asks, 'How is our data isolated from your other clients?' The answer should not be 'we use different user accounts.' It should be 'their token cannot access your schema, and your token cannot access theirs — by design, not by policy.'
The Architecture Constraint That Makes This Possible
Building in this manner requires discipline: every new feature, service, and data access pattern must honour the tenant boundary from the outset. It cannot be retrofitted. A codebase that starts with soft multi-tenancy and later adds hard isolation is not being refactored; it is being rebuilt. The decision to build this way before we had paying customers, when it was still architecturally straightforward. Multiple microservices, each with its own schema and its own gRPC interface. A token-first identity model where tenant scope is established at authentication and propagated without exception. An Envoy gateway that handles all inbound routing and enforces TLS termination before any request reaches a service.
This approach introduces real overhead. Development is slower than with a single shared data model and requires greater rigour in service communication. Every engineer must understand and respect the tenant model. The payoff is that isolation is a property of the system, not a promise the system tries to keep. For agencies operating in regulated industries, for communities handling member data, for any platform where data belonging to different organisations must never commingle — that distinction is the entire argument.
Multi-tenancy is not a feature; it is an architectural principle. The time to implement it correctly is before onboarding the first tenant, not after the tenth.